Introduction:
Modern enterprises are under a new level of scrutiny. It’s not enough to process transactions, answer calls, and conduct standard ID/V checks. They're expected to prove, pretty much at any moment, that they know exactly who they’re serving, how risky each interaction is, and whether the right safety measures are in place before any sensitive interaction takes place.
Frameworks like Know Your Customer, or KYC, are designed to make sure institutions apply the right level of control before high-risk actions take place. On paper, the logic is straightforward. In practice, it’s a lot messier.
The inbound voice channel is where many of these principles begin to break down. A large portion of callers are infrequent or first-time contacts, which means they are often not enrolled in any verification system at all. That gap creates an open door for modern fraud tactics, from social engineering to synthetic identities and increasingly convincing voice deepfakes.
In this post, we’ll explore how financial institutions currently handle compliance and security on inbound calls, where traditional methods start to show cracks, and how newer approaches are closing those gaps.
Why compliance breaks down for infrequent inbound callers
Most of the controls financial institutions use to meet KYC expectations on inbound voice calls assume repeat interaction. They work best when customers are familiar, enrolled, and call often.
That’s rarely the case for infrequent callers.
When customers reach out only occasionally, there is little opportunity to enroll them in voice-based or device-based controls. Institutions are left relying on static knowledge-based questions for the callers they know the least about. Adding more friction to compensate can slow resolution, increase abandonment, and put added pressure on agents, especially during sensitive or high-stakes interactions.
Over time, this creates a gap between the intent of risk-based assessment and what traditional voice-channel controls can realistically deliver.
Introducing Fraud Screen: a risk-based assessment layer for infrequent callers
VoxEQ Fraud Screen provides a Risk-Based Assessment (RBA) to meet compliance requirements when device registration and voice biometrics aren’t an option. It adds an early, upstream risk signal that helps institutions assess how much scrutiny is appropriate before agents proceed with the verification process.
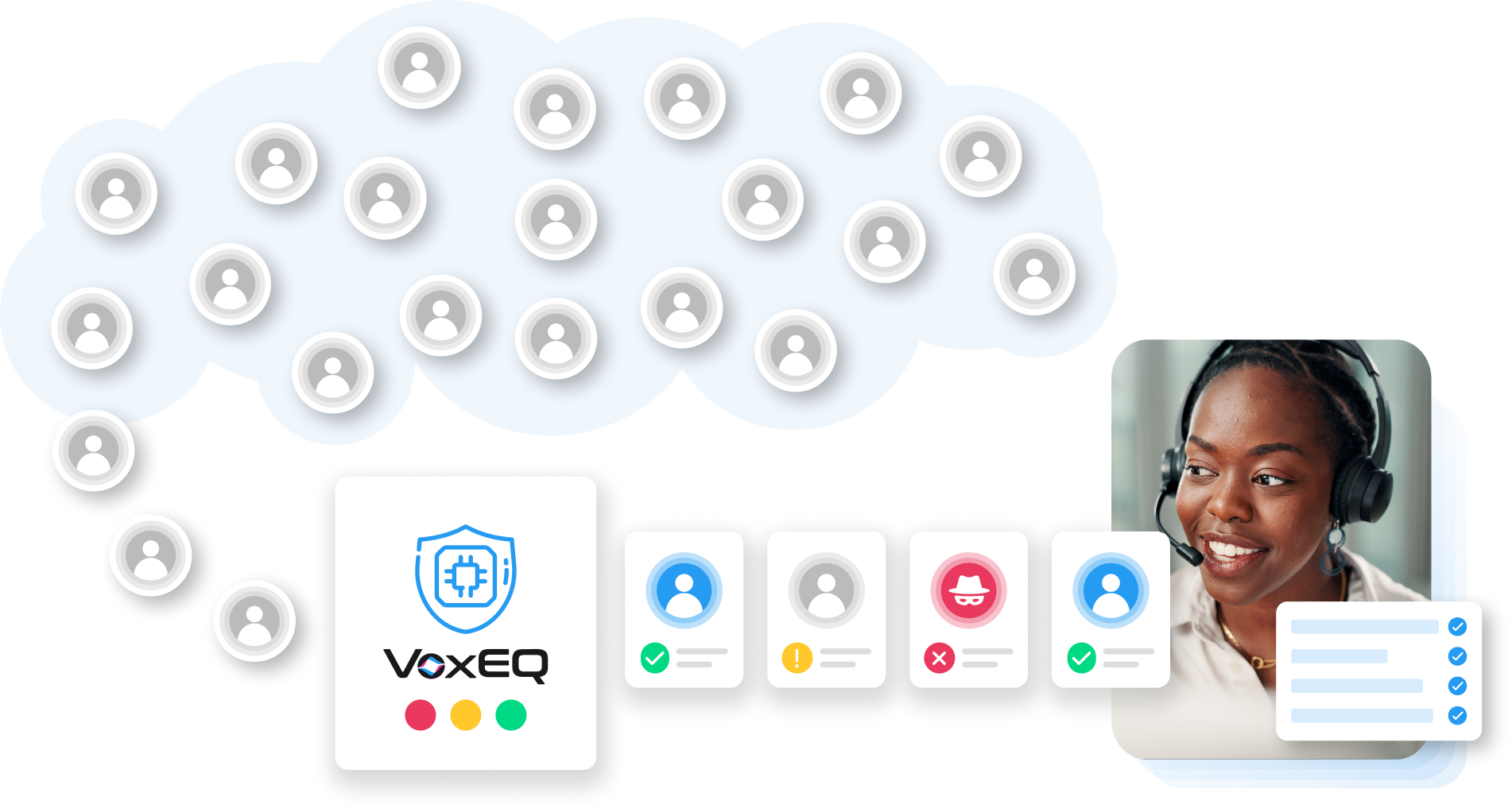
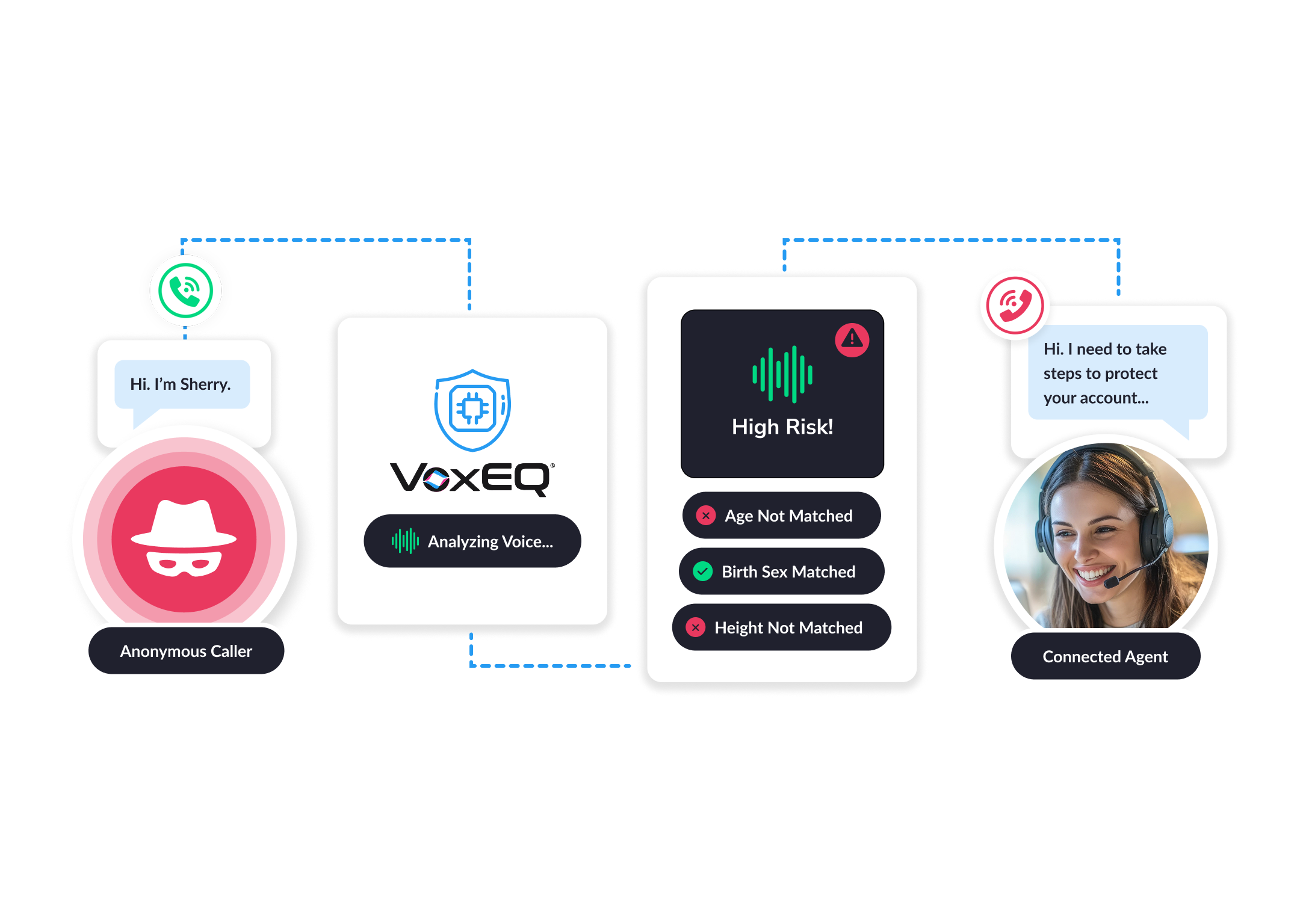
Fraud Screen analyzes bio signals in the caller’s voice to identify signs that a caller is (or is not) who they say they are, helping teams stop imposters early.
Fraud Screen doesn’t replace identification or verification, and doesn’t authenticate callers. Instead, it provides an earlier checkpoint that informs downstream decision making by providing an early risk-based assessment that helps keep fraudulent actors from even reaching the ID/V process.
This not only aligns controls with KYC expectations – it also makes sure that your agents are not relying solely on manual ID/V checks or knowledge-based questions that are prone to human error.
Benefits of Fraud Screen
Fraud Screen screens every inbound caller using voice bio-signals, without relying on security questions, passwords, or prior voice-based enrollment. That means institutions can get a fast initial risk signal that can indicate if the person calling is the approximate age and birth sex of the account holder profile that’s appearing on the agent’s screen.
When there’s evidence of a mismatch between the caller and the expected profile, institutions can flag a call as high risk, and this can be used as another layer of defense against fraudulent activity such as account takeover attempts (ATOs).
Because Fraud Screen requires no recordings, no stored files, and no back-office processes, plus it’s straightforward to deploy and maintain. It works alongside existing identity and verification systems, strengthening overall coverage without disrupting established workflows or agent processes.
By avoiding any storage of PII, Fraud Screen also helps reduce ongoing compliance and privacy exposure.
How Fraud Screen fits into the ID/V process
VoxEQ Fraud Screen sits upstream of identity and verification processes as an early screening and risk-based assessment layer. It provides an initial risk signal that helps call centers determine how much identity verification and control is appropriate before proceeding with standard authentication and servicing steps.
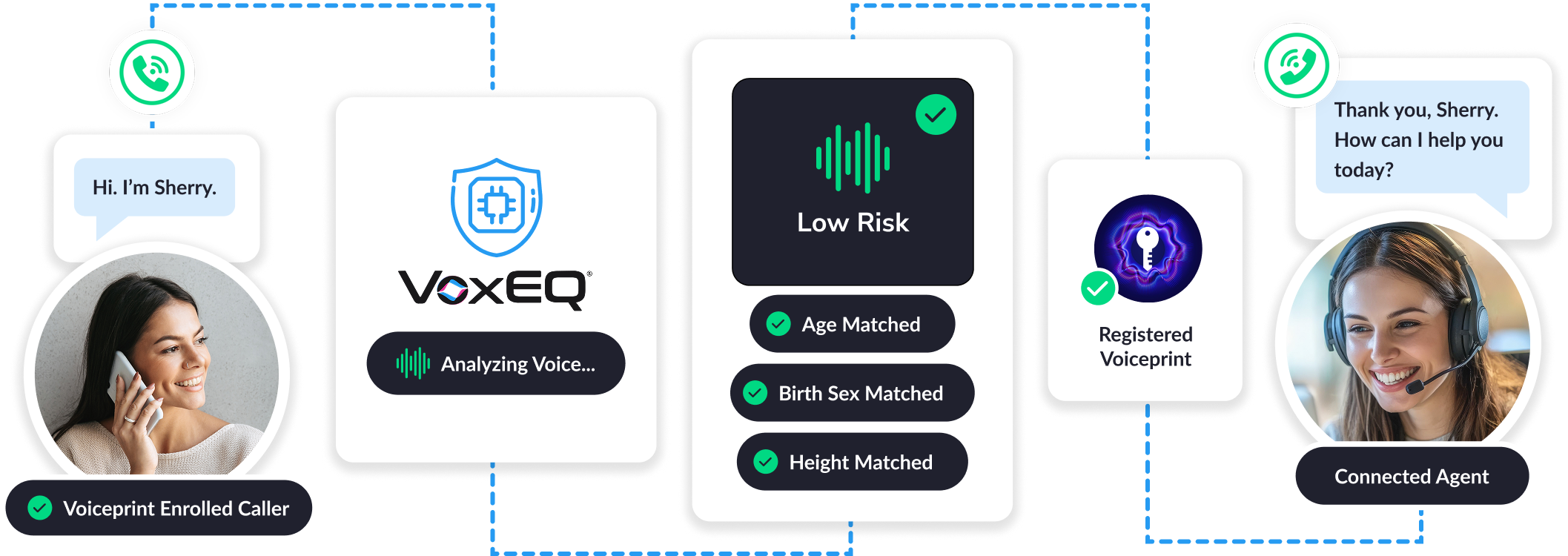
When risk appears elevated, institutions can respond by applying additional scrutiny, limiting sensitive actions, or escalating the interaction for further review.
When risk appears low, calls can proceed through existing processes without interruption. This approach allows organizations to align scrutiny with risk in a consistent, defensible way, without changing agent workflows or introducing unnecessary friction for low-risk callers.
Who Fraud Screen is for
Fraud Screen is designed for regulated environments where inbound voice interactions are infrequent, sensitive, and difficult to assess using enrollment-based controls. It's particularly valuable for teams that already have ID/V processes in place, but lack a reliable way to apply risk-based assessment early in the call.
Financial services account servicing teams
Fraud Screen supports retail banking, credit card, loan servicing, and wealth or treasury service desks, where customers often call only during life events or high-risk moments. These interactions frequently involve account changes, fund movement, or sensitive inquiries, yet provide limited historical context. Fraud Screen helps teams assess risk upfront and apply proportional scrutiny without slowing legitimate callers.
Insurance policyholder service centers
Insurance interactions such as beneficiary updates, coverage changes, claims inquiries, and renewals are typically infrequent but operationally and financially sensitive. Fraud Screen helps insurers introduce early risk assessment on inbound calls, reducing reliance on static questioning while maintaining a consistent, defensible approach to scrutiny.
Healthcare payers and health plan member services
In healthcare and health plan environments, inbound calls are often sporadic and privacy sensitive. Fraud Screen supports benefit inquiries, eligibility verification, prior authorization status checks, and billing questions by adding an early risk signal without introducing biometric storage or additional data handling complexity.
Other regulated, low-frequency scenarios
Fraud Screen is also effective in rare but high-impact interactions where additional assurance is needed without degrading the customer experience. Examples include estate and bereavement processing, beneficiary or account ownership changes, government benefits inquiries, utilities start or stop service requests, and emergency or escalation hotlines.
Across these use cases, the common challenge is the same. Institutions are expected to apply proportional, risk-based controls during interactions where enrollment is unrealistic, and context is limited. Fraud Screen helps close this gap by extending risk-based assessment to every inbound call, without changing workflows or increasing compliance exposure.
Looking ahead: a better path to improving compliance and safeguarding every caller
Across regulated industries, inbound voice interactions continue to present a difficult compliance challenge. Customers call infrequently, context is limited, and yet institutions are still expected to apply risk-based assessment and demonstrate proportional controls before sensitive actions are taken.
Fraud Screen provides a practical way to close this gap. By adding an early, privacy-safe risk signal upstream of identity and verification, institutions can extend risk-based assessment to every inbound call, including those from first-time and infrequent callers. This enables more consistent decision making, clearer alignment between risk and scrutiny, and stronger coverage without increasing operational burden.
Rather than replacing existing controls, Fraud Screen strengthens them. It allows teams to reserve added scrutiny for higher-risk interactions, while letting low-risk calls proceed normally. The result is a more balanced approach that supports regulatory expectations, protects customer trust, and reduces unnecessary friction for both customers and agents.
As regulatory scrutiny continues to increase around non-face-to-face interactions, institutions that can demonstrate clear, proportionate, and privacy-conscious risk-based assessment will be better positioned to meet compliance obligations on the voice channel, without compromising efficiency or experience.
FAQs
What is Know Your Customer (KYC), and why does it matter?
Know Your Customer, or KYC, is a regulatory requirement that means financial institutions must establish and maintain reasonable assurance that they know who their customers are and can assess the risk associated with servicing them. But KYC isn’t just about applying the same control to each interaction – it's about understanding risk proportionately. It’s why regulatory bodies such as FATF, FFIEC, EBA, and local regulators explicitly recommend risk-based controls rather than one-size-fits-all authentication. Because, as financial institutions already know, a monolithic approach just doesn’t work.
KYC typically includes three core components:
- Customer identification, verifying identity at onboarding using personal information and official documentation
- Customer due diligence, understanding the customer’s risk profile and expected behavior
- Ongoing monitoring, reviewing activity over time to detect anomalies or suspicious behavior
Risk-based assessment connects these components during live interactions. It informs how identity and access decisions are made in real time, based on factors such as the nature of the request, the customer’s history, and even voice bio-signals found in each call.
For inbound voice calls, this creates a clear operational requirement. Institutions must be able to assess risk early and determine how much confidence is required before allowing sensitive actions to proceed, even when the caller is unfamiliar or interacts only infrequently.
How financial institutions aim to meet KYC for inbound voice callers
KYC is typically enforced through a layered set of controls designed to establish confidence in a caller’s identity and assess risk before sensitive actions are taken. On the inbound voice channel, these controls are applied in combination, depending on the institution’s policies, the interaction context, and the level of perceived risk. Common control types used today include:
Knowledge-based questioning
Agents ask callers to confirm personal or account-specific information, such as date of birth, address, or recent account activity. These questions are intended to establish familiarity with the account when no other signals are available.
Automated knowledge-based flows
Interactive voice systems or virtual agents guide callers through standardized verification steps, collecting identifying details before routing to a live agent. These flows are often used to scale verification while maintaining consistency across calls.
Voiceprint-based controls
Some institutions use enrolled voice references to compare a live caller’s voice to a stored reference created during prior interactions. These controls depend on prior enrollment and sufficient call frequency to be effective.
Together, these controls are designed to support KYC obligations by combining multiple signals and applying layered scrutiny. However, their effectiveness often depends on prior enrollment, historical interaction data, or repeated customer contact, assumptions that do not hold for many infrequent inbound callers.