Financial institutions are being forced to reconcile a gap between digital and human channels. While web and mobile experiences have rapidly adopted modern authentication, the contact center remains a primary access point for high-risk interactions, often relying on weaker, legacy methods. As a result, frameworks like NIST SP 800-63 and AAL2 are no longer niche guidance. They are becoming the baseline for how organizations think about identity, access, and fraud prevention across both digital and voice-driven channels.
Credit Unions face a unique challenge as they are increasingly becoming the preferred targets of fraudsters. Bad actors are betting on a lack of sophistication within the CU and are targeting these institutions at a disproportionate rate. As a result, CUs have experienced a 55% increase in fraudulent attacks from ‘24 to ‘25 (outpacing market cohorts by 47%), and 43% of CUs reported ‘Fraud Prevention’ as their #1 technology investment (Americas Credit Unions- March 2026)
As identity systems continue to modernize, much of the industry has rallied around NIST SP 800-63 as the foundation for digital trust. Within that framework, Authenticator Assurance Level 2, or AAL2, has emerged as the practical standard for balancing security and usability. It is strong enough to mitigate most forms of identity theft, yet flexible enough to work across large and diverse user populations.
At a high level, AAL2 is designed to answer a simple but critical question. Is the person authenticating right now the same person who originally enrolled? The mechanism for answering that question is multi-factor authentication, requiring at least two different types of signals. These typically include (1) something you know, (2) something you have, or (3) something you are.
Voice biometrics have naturally found a place within this model although not widely used in CUs due to cost and scale. As an inherence factor, the human voice offers a low friction, intuitive way to authenticate users, particularly in channels like call centers where traditional authentication methods introduce both friction and vulnerability. Whether active, where users repeat a phrase, or passive, where speech is analyzed during conversation, voiceprints provide a compelling way to bind a user to an identity.
Beyond legacy voiceprints, modern voice profile analysis looks at the acoustic characteristics of speech. Now it is possible to infer attributes such as approximate age range, birth sex, and other physiological markers embedded in the voice. These signals are not deterministic identifiers in the same way a voiceprint is, but they provide something equally valuable. They provide context. They allow the system to evaluate whether the current interaction aligns with what is known about the user.
For example, a voiceprint may match a previously enrolled user, but the inferred age may be significantly different, or the vocal characteristics may suggest a different birth sex profile. On their own, these discrepancies may not definitively prove fraud but taken together they form a meaningful anomaly signal.
This kind of signal does not replace AAL2 requirements, nor does it function as a standalone authentication factor under NIST definitions. Instead, it operates as a complementary layer that strengthens the integrity of the authentication process by introducing a plausibility check alongside traditional factors.
That distinction matters. NIST defines the minimum bar for assurance, not the ceiling for innovation. The organizations that are most resilient to fraud are not stopping at compliance. They are building additional intelligence around these frameworks.
Demographic voice analysis fits naturally into this shift toward risk-based and adaptive authentication. When a system detects a mismatch between expected and observed voice characteristics, it can respond dynamically. It may trigger step up authentication, require additional verification, or flag the interaction for further review. Authentication becomes less of a binary pass or fail decision and more of a continuous evaluation of risk.
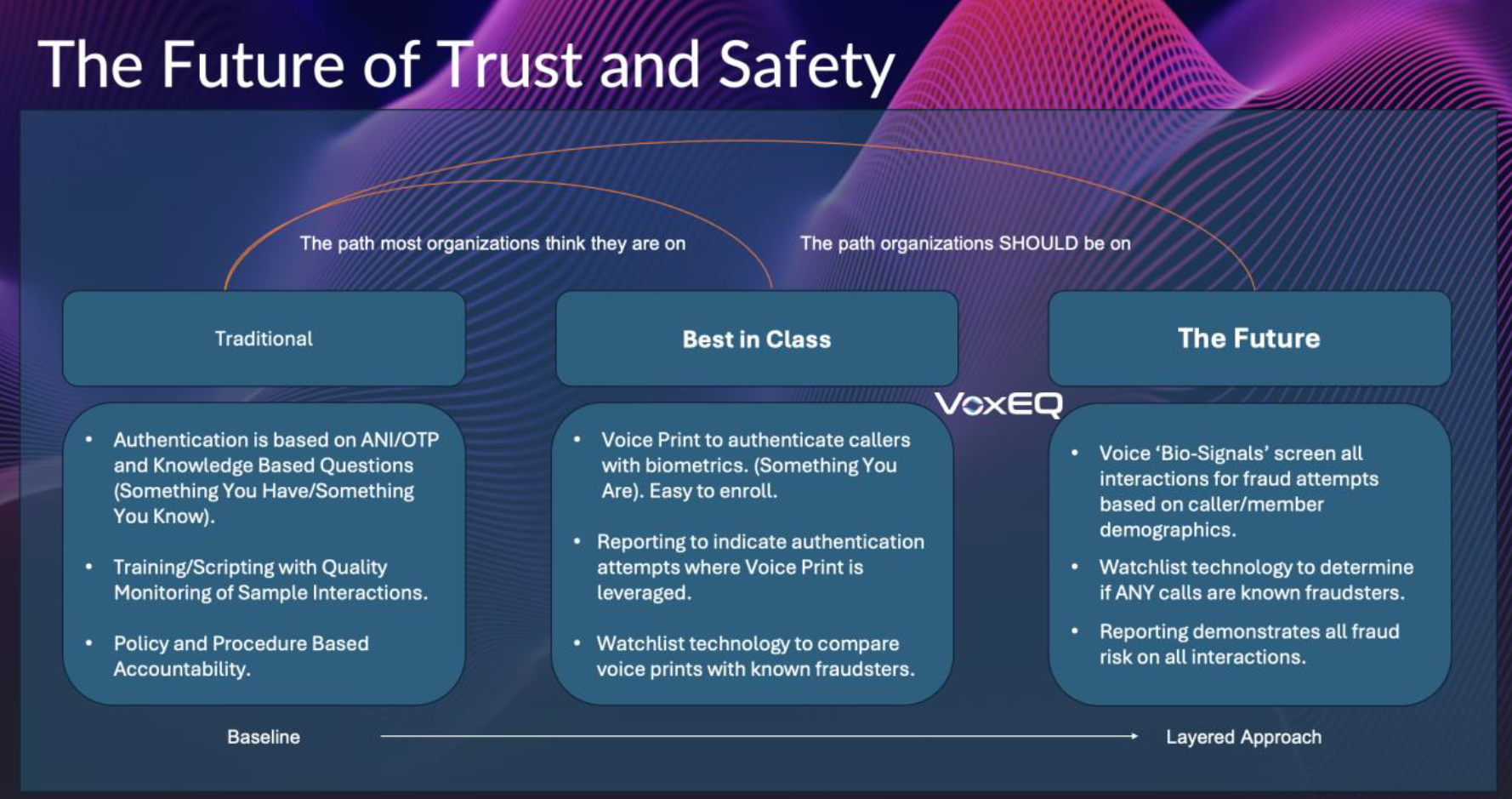
The Future of Trust and Safety
This shift is especially important in CUs, where the cost of identity compromise is high (member centric), and the attack surface continues to expand. Credential theft, social engineering, and now, AI driven scale are converging in ways that traditional controls were not designed to handle.
What emerges is a more layered model of identity assurance. Voiceprints continue to serve as a valuable inherence factor, confirming that the voice is consistent with prior interactions. Demographic inference adds a second dimension, validating that the voice is plausible for the identity. Together, they create a stronger defense than either could provide alone.
From a strategic standpoint, this combination reflects a broader shift in how authentication is being approached. The goal is no longer just to verify possession of credentials or match a biometric pattern. The goal is to establish confidence that the person on the other end of the interaction is authentic in a more complete sense, consistent, plausible, and aligned with what is known about the identity over time.
AAL2 remains an essential foundation for achieving that goal. But as the threat landscape evolves, it is becoming clear that compliance alone is not enough. The next generation of identity systems will be defined not just by the factors they require, but by the intelligence they apply in interpreting those factors.
In that context, voice biometrics are a critical requirement for today’s CU marketplace. They are simply incomplete on their own. When combined with deeper analysis of the voice itself, they become part of a more resilient and adaptive approach to identity verification.
Ultimately, the question is shifting. It is no longer sufficient to ask, did this user pass authentication. The more important question is, does this interaction genuinely represent the person behind the identity.
Answering that question requires moving beyond static signals and toward a richer understanding of human authenticity, something the voice, when fully analyzed, is uniquely positioned to provide.